Reading Time: 20 minutes
Difficulty: Easy (though dry)
Pre-requisites : none
The U.S. government and its cornucopia of agencies and departments is both vast and complicated. Combine that morass with the already jargon-heavy technology sector and you’ve got a stew of acronyms and abbreviations that are difficult to parse, let alone understand.
This article clarifies two important Federal standards: FedRamp and the DISA SRG. We explore why they exist, what they are, how are they different, and the various organizations and products used to create these standards. After reading this article, you can dazzle friends with your knowledge of the general flow and relationships that exist between these standards. Imagine their delight!
But seriously, after this article you should be able to read something official like https://www.fedramp.gov/assets/resources/documents/FedRAMP_Policy_Memo.pdf and follow it, understanding the relationships and players (if you want to check your comprehension – this is a good test).
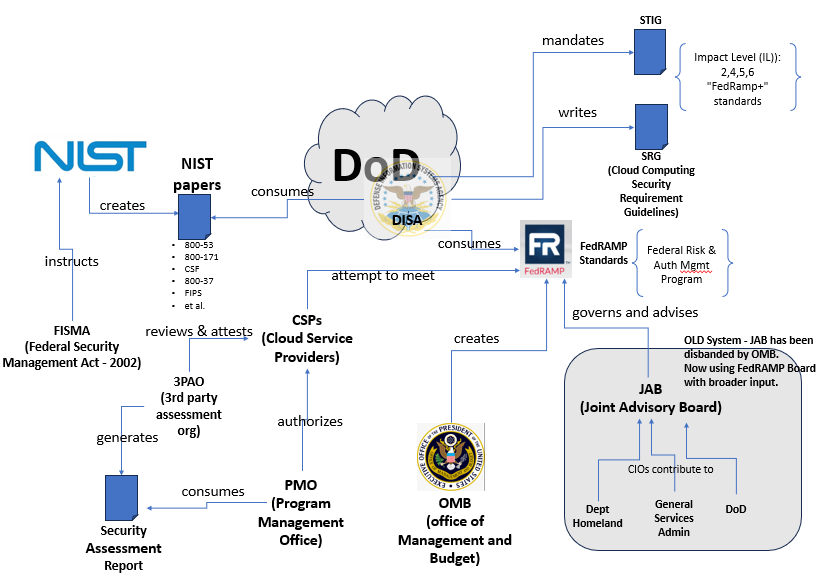
Pictorial Relationship
The picture below is an overview of the FedRAMP and DISA compliance ecosystem. Hold tight though – it’s a doozy. Don’t you worry though, we’re going to explain it by starting small and gradually adding items in one at a time. For now, just peruse the diagram; no need to spend too much time on it. It’s here for reference as we fill-in the puzzle piece-by-piece.
Click on the picture to expand it – or open it in a separate tab to reference it while reading. We will start with some of the logos on the right and work our way through the puzzle:
In the beginning…there is FISMA and it is good
In 2002, the internet was still relatively young. Cloud computing had not yet been invented, but unfortunately cyber crime had. With U.S. government agencies becoming increasingly interconnected and reliant on the internet it was evident that, even at this early stage, cybersecurity was essential. However, the patchwork security measures implemented piecemeal by each government agency were disorganized and incomplete.
Enter FISMA: The Federal Information Security Management Act of 2002 (and later revised in 2014). It mandated a unified approach to information security for federal agencies. Instead of a fragmented collection of independently developed security protocols FISMA called for a comprehensive, centrally managed, set of guidelines to rule federal all agencies.
Under FISMA, the National Institute of Standards and Technology (NIST) was tasked with developing a cohesive framework that would standardize cybersecurity practices across the government. Additionally, the Office of Management and Budget (the OMB) was responsible for overseeing and administering the agencies and that would build these new guidelines and standards. From FISMA, FedRAMP was born.
Enter “The Cloud”
Though FISMA pre-dated cloud computing, the standards – both FedRAMP and DISA SRG – are specific to Cloud Service Providers (CSPs). The FISMA coverage is broad – giving advise for any government system – but the standards themselves are cloud-based.
Cloud providers, like AWS, Microsoft Azure, and Google, work hard to create frameworks that adhere to these standards and certifications – implementing (and allowing others to implement) Cloud Service Offerings (CSOs) that meet the government standards. Users of these clouds will no doubt have seen mention of FedRAMP-specific offerings and the FedRAMP-specific cloud.
The Players
Before we launch into some of the details, let’s take a moment to meet the key players. These organizations contribute to the majority of the security standardization process.
They are:
- NIST – National Institute of Standards and Technology. The “standards” guys – specializing in creating publications and official standards of all types..
- OMB – the Office of Management and Budget. The administrator and overseer of the FedRAMP structure and involved agencies. They provide over-arching guidance to the structure of FedRAMP.
- DISA (and DoD) – Defense Information Systems Agency. They consume much of the same content (like NIST publications) but create their own security standards for the Department of Defense (DoD). They own and govern the DISA SRG standard.
- CSP (and CSO)– Cloud Service Provider. The cloud provider implementing the system (or underlying system) on which the certified security offering (CSO) is created. Often times this is AWS, Azure, or GCP, though many other cloud providers exist.
- GSA – Government Services Administration. A government agency that contains many of the other security-specific and FedRAMP-centric groups, like the FedRAMP board and the PMO.
- FedRAMP Board – A group of individuals selected by the OMB that write and codify the FedRAMP standards.
- PMO – Program Management Board. This group is responsible for the certification process. Once a system gets pre-approval, then the PMO determines the official suitability of whether or not a CSO receives certification. The PMO is sub-division of the larger Government Services Administration.
NIST
If you need standards—real standards—NIST is the organization for you. NIST sets standards for all manner of important topics – from codifying measurements like timekeeping to providing guidance for global industries and scientific research. NIST’s expertise in handling complexity and driving cross-agency standardization was the reason why FISMA selected the agency for cyber security best practices.
Following the FISMA directive, NIST began developing a series of papers outlining best-practice standards for all aspects of computing and security, including encryption, digital forensics, cyber detection and response, among others. Today, NIST provides guidance on nearly every aspect of computer and information security—and its coverage continues to expand to meet the changing landscape.
Here are a few of the NIST URLs that categorize their security guidance publications (note: these are broad categories of papers – not the papers themselves):
| Special Publications (SP) – 800 Series – Security Guidance | https://csrc.nist.gov/publications/sp800 |
| Special Publications (SP) – 1800 Series – Cybersecurity Practice Guides | https://csrc.nist.gov/publications/sp1800 |
| (CSWP) – Cybersecurity Whitepapers | https://csrc.nist.gov/publications/cswp |
NIST produces thousands of detailed papers covering every aspect of security. Among all these, some are meant to be foundational to systems development and compliance. These keystone documents help structure many of the more specialized publications.
Examples include:
- 800-53a Rev5: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-53r5.pdf (security and privacy controls)
- 800-53B: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-53B.pdf (categories and controls of security and privacy in systems)
- 800-37: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-37r2.pdf (system life-cycle approach to building and securing systems)
- 800-171: https://csrc.nist.gov/pubs/sp/800/171/r2/upd1/final (controlling sensitive information)
Note that these papers are constantly shifting and changing – as the world of cybersecurity and cyber-crime [espionage, terrorism, nation-state threat actors, etc.] evolve and push governments to adapt. It is a full-time job keeping up with the Jones’ and the ever-shifting landscape of security.
OMB
FISMA tapped NIST for defining the initial set of best practices, but there was also a need to oversee and administer the on-going standard. The Office of Management and Budget (the least sexy sounding agency name?) is the department that does this for FedRAMP. They pull in other agencies as needed to keep FedRAMP moving forward.
PMO
The Program Management Board is a sub-division of the Government Services Administration. They are the group that creates and oversees the certification process. It grants candidate CSPs and CSOs certifications against the FedRAMP standard and its various levels.
Department of Defense and DISA
The vast Department of Defense has, within it, a sub-organization called Defense Information Systems Agency. It provides communications and IT support to the military. DISA consumes much of the information coming from NIST (along with other sources) and evaluates it through its military-specific lens making sure that the doctrine and regulation meet the rigor needed for military secrecy.
DISA creates, as output, its own guidance – similar to NIST but with a military-based slant. These papers are called “SRG” (Security Requirement Guides) and span all the topics one would expect from a military complex. They control the administration and certification against the SRG standard – taking on the role that the OMB and the PMO play for FedRAMP.
The Standards: FedRAMP, and DISA SRG
Simply put, FedRAMP and DISA SRG are two different standards that the government uses to ensure that computer information systems are secure.
- FedRAMP – Federal Risk and Authorization Management Program provides a framework for all federal agencies to secure their systems and data. This standard is divided into several levels based on data sensitivity (Low, Moderate, High) with security requirements becoming more restrictive as sensitivity increases (more about this below).
- DISA SRG – Defense Information Systems Agency – Security Requirement Guide is similar to FedRAMP but designed specifically for the military. While it follows a separate, military-focused standard, it incorporates much of the same data to establish security levels from 1 to 6 (though some levels are not used, as we’ll see later).
These two standards influence and complement each other. Each has its own certification process: FedRAMP using the PMO and SRG using DISA. Achieving a certification qualifies the candidate system or cloud service offering (CSO) for government use. Once certified, that system is then allowed to work-with and interoperate-with government agencies. This often means that public companies (building the candidate system) can then pursue government contracts.
Since the U.S. Government is the largest company within the domestic U.S., it’s no surprise that companies try hard to compete for government contracts. Though daunting at the outset, securing a government contract can provide a company with a healthy revenue stream that is both stable and long-lasting.
FedRAMP Details:
- Levels: Low, Moderate, and High
- Standards based largely on NIST publications but others as well (the PMO decides what references best suit the final standard)
- Administered by the OMB; Run by the PMO
- Scope includes all federal government agencies
Here is a overview of the FedRAMP levels:
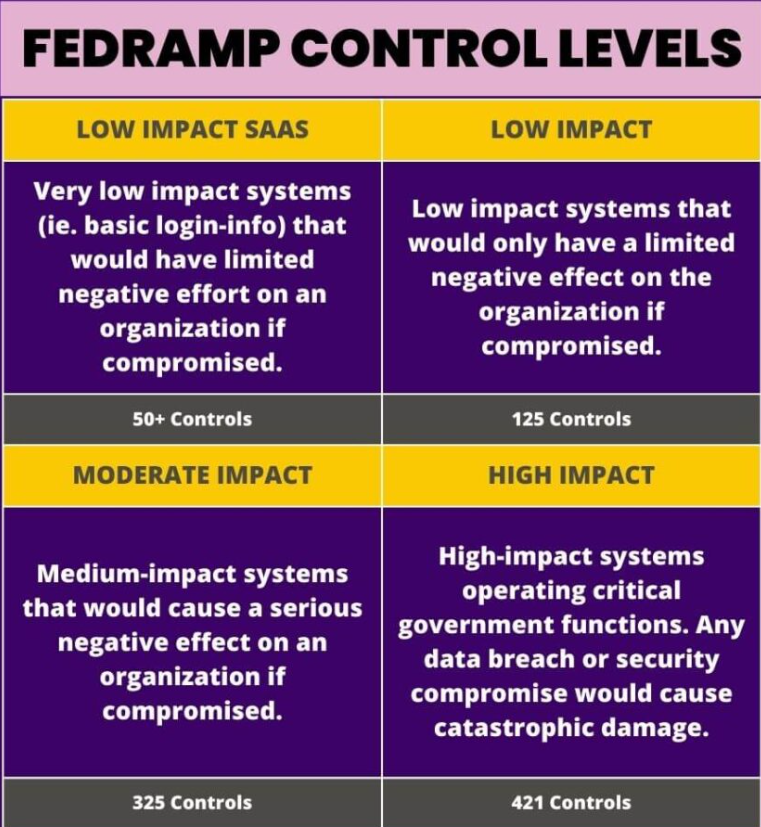
The “controls” referenced above are security requirements for the candidate system. Achieving FedRAMP compliance earns the qualifying company the ability to hunt contracts from all manner of federal agencies: USDA, Department of Interior, FDA, and Department of Homeland to name a few.
DISA SRG Details:
- Levels: Impact Levels (IL) according to sensitivity: 2,4,5,6 (1 and 3 are not used and are “rounded-up” to the next higher level)
- Based largely on NIST and FedRAMP with additions and modifications to support the military
- Also called: FedRAMP+
- Scope is focused on U.S. Military agencies and operations
Here is a synopsis of the DISA Impact Levels:
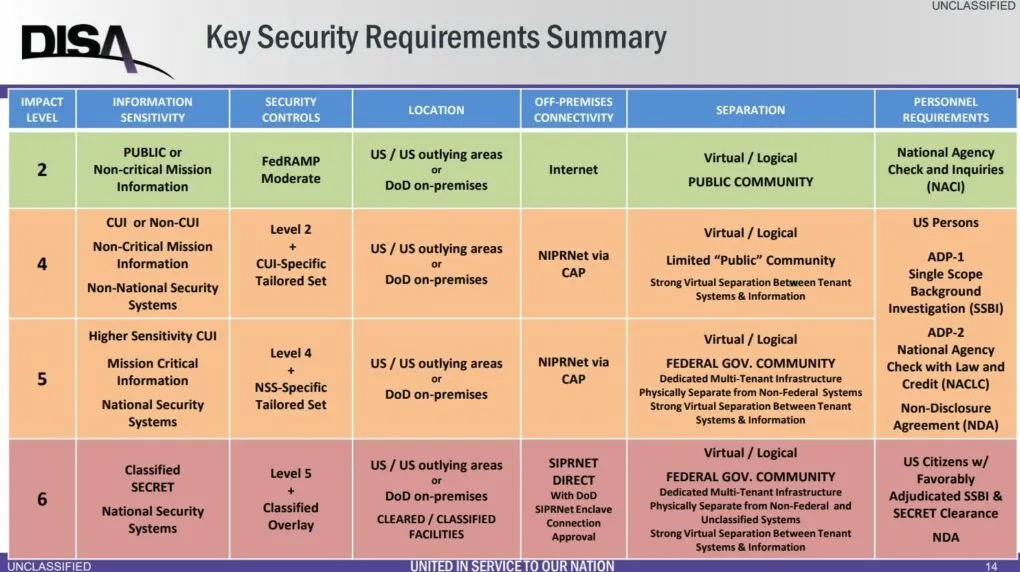
The DISA requirements are broken out into these general categories:
- Access Control
- Awareness and Training
- Audit and Accountability
- Security Assessment and Authorization
- Configuration Management
- Contingency Planning
- Identification and Authentication
- Incident Response
- Maintenance
- Media Protection
- Physical and Environmental Protection
- Planning
- Personnel Security
- Risk Assessment
- System and Services Acquisition
- System and Communication Protection
- System and Information Integrity
- Supply Chain Risk Management (new with Revision 5)
These control categories are similar to the FedRAMP “controls” listed above.
Meeting a DISA SRG impact level allows that company to compete in defense contracts and defense-related missions. Today, DISA is led by General Stanton from the Department of Defense Information Network (DDIN). More here: https://public.cyber.mil/dccs/.
The DISA SRG and STIG
The SRG are requirement publications that DISA creates for candidate systems. Many manufacturers consume these requirements and give specific guidance on how you can use their devices or systems to meet the SRG requirements. These are called STIGs: Security Technical Implementation Guides. For example, a Juniper switch that is used as part of a DISA IL-5 solution would specify how to configure and operate that particular device (like an EX switch) to meet the SRG requirements.
The STIGs are written by the manufacturers (Juniper in our example) to provide make and model specific configuration guidance for that device’s secure use. If your feeling particularly interested, you can navigate and peruse STIGs (and SRGs) here: https://public.cyber.mil/stigs/compilations/.
Compliance
Compliance is established when a CSP, or CSP-based company, reaches out and starts the lengthy process of getting certified. Included in the process are several documentation packages (e.g., a Security Assessment Report – SAR) that need to be created and reviewed. The certification process uses specialized third-party assessment organizations (3PAO) to collect and pre-approve a system’s adherence to the standard (FedRAMP or DISA) based on the level being sought.
Once all the documentation is collected and pre-approved by the 3PAO, it is officially submitted for PMO approval.
In the end, if all is successful authorization is given with a Provisional Authority to Operate (P-ATO). At this point the CSO is cleared for government use. Note that some requirements for on-going monitoring and re-certification exist – making sure that the system is keeping up to date with evolving regulations.
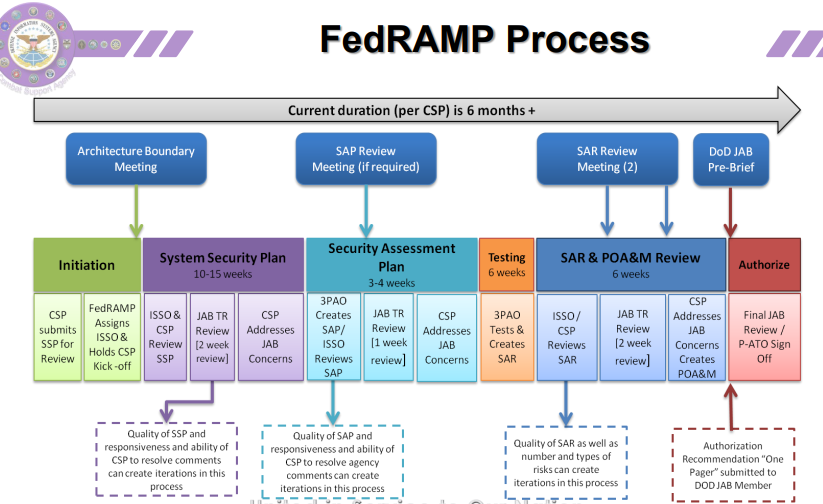
The DISA certification process is similar to the FedRAMP one. It can be viewed here:
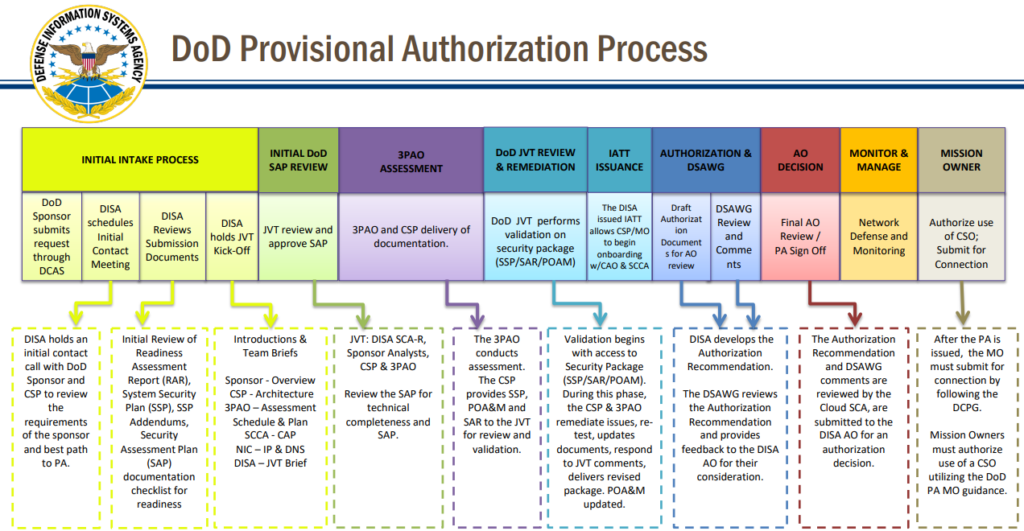
Source: https://dl.dod.cyber.mil/wp-content/uploads/cloud/pdf/unclass-dod_cloud_authorization_process.pdf
DISA largely uses the FedRAMP certification process and the information presented collected for FedRAMP certification to do its own review.
Other Terms and Players
When talking about FedRAMP and DISA you’re likely to come across a few other terms and organizations that you may want to know. These include:
- FIPS – Federal Information Processing Standards (FIPS) are a set of guidelines and standards developed by the National Institute of Standards and Technology (NIST) that define security requirements for computer systems used by U.S. federal agencies, ensuring consistent data protection and interoperability across government systems; essentially, they set the bar for how sensitive information is handled within the federal government, covering aspects like encryption algorithms and data security protocols.
- CISA – The Cybersecurity and Infrastructure Security Agency (CISA) is a U.S. government agency that protects critical infrastructure from cyber and physical threats. CISA also provides cybersecurity services and resources to the public. Similar to NIST, they review and recommend security best-practices for all – including government, private-sector, and individual users. They also track the vulnerabilities that are popping up.
- CVE – Common Vulnerabilities and Exposures. These are specific technical security exploits that have been discovered and documented.
- CWE – Similar to CVEs, but these are broader areas of weaknesses that might attract vulnerabilities or exploits in security.
- CMMC – The Cybersecurity Maturity Model Certification (CMMC) is an assessment framework developed by the U.S. Department of Defense (DoD). The primary objective is to enhance the cybersecurity controls that are in place for organizations supplying the DoD, known as the Defense Industrial Base (DIB). The CMMC model aims to manage risk and verify that DoD contractors can safeguard information classed as Controlled Unclassified Information (CUI) and comply with NIST SP 800-171 DOD assessment requirements and some other cybersecurity requirements.
Wrap-up
While its doubtful that you’re now a federal compliance expert – you should have a basic knowledge of the governmental agencies, regulations, and processes used by FedRAMP and DISA. Now invite those friends over so you can tell them all about it! They’ll be so happy you did.
Seriously though – try opening up the link below, flip to a random page, and test to see if you understand its content. If you do, give yourself a pat on the back – you did it!
https://www.fedramp.gov/assets/resources/documents/FedRAMP_Policy_Memo.pdf
Thanks for reading!